On Tuesday, the US Department of Justice charged two Chinese nationals with allegedly hacking hundreds of organizations and individuals in America and elsewhere to steal confidential corporate secrets on behalf of Beijing for more than a decade.
The pilfered files are said to be worth hundreds of millions of dollars, and in some cases, it is claimed, the pair tried to extort money out of their victims: pay up, or the trade secrets leak.
The targeted organizations are said to include a British AI and cancer research biz, an Australian defense contractor, a South Korean shipbuilder and engineering giant, German software makers, American pharmaceutical, software, and defense corporations, and the US Dept of Energy’s Hanford site.
Assistant Attorney General John Demers and other US officials held a press conference on Tuesday to unseal the 11-count indictment [PDF], returned by a grand jury on July 7, against Li Xiaoyu, 34, and Dong Jiazhi, 33.
“The campaign targeted intellectual property and confidential business information held by the private sector, including COVID-19-related treatment, testing, and vaccines,” said Demers in prepared remarks.
“The hackers also targeted the online accounts of non-governmental organizations and individual dissidents, clergy, and democratic and human rights activists in the United States, China, Hong Kong, and abroad.”
According to the indictment, Li and Dong, former classmates at an electrical engineering college in Chengdu, China, have been hacking into high tech manufacturing, civil, industrial, and medical engineering firms, software companies of all sorts, solar companies, and pharmaceuticals, among others, since 2009.
The US claims that the two accused worked both for themselves and with the backing of the Chinese government’s Ministry of State Security. This assistance included being supplied with zero-day vulnerabilities exploits to facilitate their intrusion.
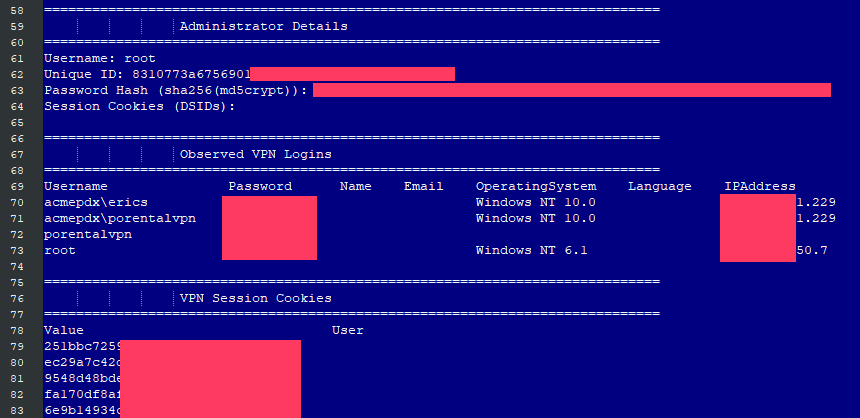
But often their hacking sprees, it’s alleged, involved the exploitation of publicly known vulnerabilities. The accused hackers are said to have used a program called China Chopper to install web shells to execute commands on victims’ networks and exfiltrate documents. The duo also uploaded password-stealing malware, it is claimed.
The pilfered data, it’s claimed, was often packed up on the RAR archive files that were concealed through the use of innocuous file names and common file extensions like .jpg. The hackers are said to have frequently used the recycle bin on Windows machines to store and move files because administrators are less likely to look there.
Adding insult to injury
“The defendants stole hundreds of millions of dollars’ worth of trade secrets, intellectual property, and other valuable business information,” the indictment says.
“At least once, they returned to a victim from which they had stolen valuable source code to attempt an extortion – threatening to publish on the internet, and thereby destroy the value of, the victim’s intellectual property unless a ransom was paid.”
The indictment also accuses the pair of providing Chinese authorities with the passwords of email accounts belonging to Chinese dissidents and to academics in the US and other countries.
Recently, Li and Dong are said to have been researching vulnerabilities in the networks of biotech firms involved in COVID-19 vaccine research. It’s claimed they have gone after organizations and individuals in the United States, Australia, Belgium, Germany, Japan, Lithuania, the Netherlands, Spain, South Korea, Sweden, and the United Kingdom.
“China’s anti-competitive behavior and flagrant disregard for their promises not to engage in cyber-enabled intellectual property theft is not just a domestic issue; it is a global issue,” said Demers.
The defendants have each been charged with one count of conspiracy to commit computer fraud, theft of trade secrets, wire fraud, and unauthorized access of a computer, and with seven counts of aggravated identity theft.
China has no extradition treaty with the US, and relations between two countries are not particularly cordial at the moment, which makes it highly unlikely either of the two defendants will ever appear in a US courtroom unless they get really stupid crossing borders. That seems unlikely now.