Analysis of tracking data from Automatic Identification System broadcasts reveals vessel locations have been simulated for a number of ships, including military vessels. This false information could compromise vessel safety, decrease confidence in a crucial collision avoidance system and potentially spark international conflict.
Over the years, data analysts working with Global Fishing Watch and SkyTruth have noticed a number of ship tracks coming up in impossible locations—in transit over Antarctica, circling in the Utah desert and elsewhere—and we have questioned whether these false positions resulted from faulty Automatic Identification System (AIS) transmitters, deliberate misuse of those transmitters, or from intentional third party interference. AIS is the international system of vessel radio broadcasts used to identify vessel locations and help prevent collisions at sea. We have learned how to interpret anomalies in AIS data and, even when the ship coordinates were wrong, we never had reason to doubt that these vessels were on the water broadcasting AIS. In most cases, we are also able to identify the true position of the vessel.
[…]
I first noticed these false AIS tracks in groups of sailboats which appeared hundreds of miles out in the Atlantic Ocean even though shore-based AIS antennas appeared to receive their positions. Since a typical range for a terrestrial antenna is at most about 60 miles, I knew something was wrong with these positions. When I searched for more information on the identities of these vessels I found that they were featured on a website running simulated sailing races. Whoever was setting up the races not only simulated realistic AIS positions for each of the participants, but then fed these made up positions into a public AIS site — sites like AISHub receive ship positions from contributors — so that the sailboat positions appeared on these sites alongside real vessel traffic.
[…]
Our recent investigation into a second group of false AIS tracks has shown that these concerns were very much warranted. I was alerted to this case when an article in Dagens Nyheter, a Swedish news outlet, was shared with me. Nine Swedish Navy vessels appeared on AIS as if out on maneuvers. In the news story, the Swedish Navy confirmed that these positions were false and mentioned additional false positions in the Baltic Sea, specifically near the Russian enclave of Kaliningrad.
[…]
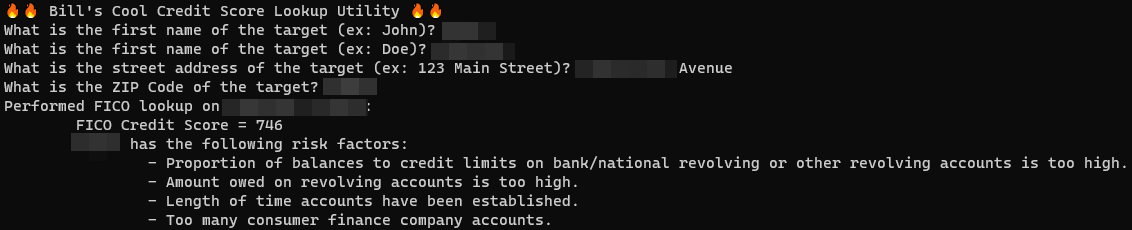
I was able to take advantage of the full complexity of AIS communication to identify a pattern specific to the false simulated AIS positions. From there, I wrote an automated computer query of our global AIS database to identify other vessels with this same pattern of AIS broadcast.
The results were alarming. Nearly a hundred U.S. and European naval vessels had track segments with the same AIS pattern as the false tracks of the Swedish navy ships near Karlskrona. Over the past few months I dug into this data using all available sources to confirm vessel locations and identities. I confirmed false AIS positions for 15 navy vessels from seven countries, with many more vessels suspected of having fabricated positions.
[…]
Naval vessels are frequently photographed, and it’s possible to get a sequence of port visits based on photos uploaded to sites like warshipcam.com. This documented series of port visits can then be compared to the AIS track to confirm that an MMSI corresponds to a particular vessel.
[…]
Two sources of open satellite imagery work very well for matching to AIS, Sentinel-1 (S1) synthetic aperture radar (SAR) and Sentinel-2 (S2) optical imagery from the European Space Agency (ESA). S1 SAR is acquired with very high frequency over Europe — any given location is imaged approximately every other day and has the advantage of penetrating clouds
[…]
I matched S1 and S2 imagery to tracks of 15 naval vessels with AIS patterns sharing characteristics identified in the false positions of the Swedish vessels near Karlskrona. These 15 examples, which I was able to confirm with comparison to imagery, represent just a fraction of the nearly 100 naval vessels with suspected false AIS tracks identified by my algorithm between August 27, 2020 and July 15, 2021.
[…]
I describe two examples below.
U.S. survey vessel USNS Bruce C. Heezen transiting into Baltic Sea, September 2020
AIS data shows this vessel transiting through the North Sea and entering the Baltic Sea between September 17 through 23, 2020. However, the positions broadcast on those dates match the false AIS pattern, and I have additional evidence that this AIS track did not show the actual location of the vessel.
[…]
British Aircraft carrier HMS Queen Elizabeth on the Irish coast with accompanying flotilla of British, Dutch, and Belgian warships, September 2020
AIS from September 17, 2020, shows a surprising international naval flotilla accompanying the British aircraft carrier HMS Queen Elizabeth about 20 miles out from the coast of Ireland. In addition to the 283-meter Queen Elizabeth, AIS shows the British HMS Duncan (152 meters) and HMS Albion (176 meters) as well as the Dutch HNLMS Rotterdam (163 meters), the HNLMS Johan de Witt (176 meters) and the Belgian BNS Leopold I (122 meters). This flotilla of massive warships should have made quite a striking picture on Sentinel-2 satellite imagery. However, the image coinciding with the AIS transit dates, seen below, shows none of the six naval vessels. Furthermore, several publicly posted photos and news articles show that these vessels were in port elsewhere at the time.
[…]
It’s unclear how the false positions get combined with real data from terrestrial AIS antennas, though one can hypothesize that they could be produced by an AIS simulator program similar to that used to produce the tracks in the simulated sailing races. While I initially thought the false data might be entering the data feed from a single terrestrial AIS station, it appears that false AIS positions were reported at a number of different terrestrial stations.
Some of these terrestrial stations appear to be picking up AIS positions when vessels are too far away. For example, a suspected false position near Kiel, Germany was picked up by a receiver in Gdynia, Poland more than 300 miles away and outside of normal terrestrial antenna range. However in other cases, false positions were picked up by nearby receivers. Further information linking individual AIS positions to particular receiving antennas could allow us to understand more about where the positions are coming from.
Possible motives for data falsification
It’s clear that considerable care was taken to produce plausible tracks. For example, false AIS segments mostly appear only in those locations where naval vessels would be expected to broadcast AIS (near port and in other congested areas). Confirmed and suspected false AIS segments show incursions by 11 North Atlantic Treaty Organization (NATO) and NATO allied warships into Russian territorial waters near Kaliningrad and Murmansk as well as within the disputed territorial waters around Crimea in the Black Sea. Suspected false tracks from June 2021 also show two Russian warships entering the territorial waters of Ukraine and Poland. Other false AIS tracks are more subtle
[…]
A recent incident in the Black Sea shows how uncomfortably close we are to a scenario where a false AIS track is used to show an aggressive action by a naval vessel that did not really occur. From June 18 to 19, 2021, the British destroyer HMS Defender and Dutch frigate HNLMS Evertsen could be seen at dock in Odessa, Ukraine. However, on those same dates, AIS showed the vessels leaving port and going to a naval base in Sevastopol in Russian-occupied Crimea.
[…]
Although this attempt at disinformation was easily refuted by witnesses and a live webcam in Odessa, a far more delicate situation unfolded a few days later when the HMS Defender really did leave Odessa and transit through Russian claimed waters. The HMS Defender broadcast AIS during the transit past Crimea that showed the vessel entering disputed territorial waters that extend 12 nautical miles from shore. The vessel entered only about 1.8 nautical miles inside territorial waters and maintained a normal transit course under “innocent passage.” Russian forces claim to have responded with warning shots and dropping live bombs in the path of the vessel. The HMS Defender proceeded normally, exiting the waters around Crimea and continuing to Georgia.
[…]
Fortunately, these false tracks could be readily identified with the same systematic data analysis tools which have made it possible to pull increasingly detailed information from the global AIS dataset to inform researchers about activity at sea.
The openness and accessibility of AIS has made possible innovative uses of the data. But this accessibility also makes the system vulnerable to manipulation which, if not detected, could support false narratives about vessel movements that cause confusion and potentially could even spark an international incident.
Ultimately, AIS is a critical collision-avoidance system relied upon by thousands of mariners, and while these manipulations don’t directly compromise on-the-water collision avoidance, they may compromise trust in the AIS system
[….]