Eggheads at the University of Michigan in the US, and Zhejiang University in China, have found that hard disk drives (HDDs) can be turned into listening devices, using malicious firmware and signal processing calculations.
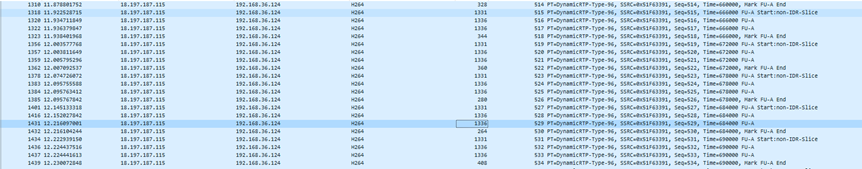
For a study titled “Hard Drive of Hearing: Disks that Eavesdrop with a Synthesized Microphone,” computer scientists Andrew Kwong, Wenyuan Xu, and Kevin Fu describe an acoustic side-channel that can be accessed by measuring how sound waves make hard disk parts vibrate.
“Our research demonstrates that the mechanical components in magnetic hard disk drives behave as microphones with sufficient precision to extract and parse human speech,” their paper, obtained by The Register ahead of its formal publication, stated. “These unintentional microphones sense speech with high enough fidelity for the Shazam service to recognize a song recorded through the hard drive.”
The team’s research work, scheduled to be presented in May at the 2019 IEEE Symposium on Security and Privacy, explores how it’s possible to alter HDD firmware to measure the offset of a disk drive’s read/write head from the center of the track it’s seeking.
The offset is referred to as the Positional Error Signal (PES) and hard drives monitor this signal to keep the read/write head in the optimal position for reading and writing data. PES measurements must be very fine because drive heads can only be off by a few nanometers before data errors arise. The sensitivity of the gear, however, means human speech is sufficient to move the needle, so to speak.
“These extremely precise measurements are sensitive to vibrations caused by the slightest fluctuations in air pressure, such as those induced by human vocalizations,” the paper explained.
Vibrations from HDD parts don’t yield particularly good sound, but with digital filtering techniques, human speech can be discerned, given the right conditions.
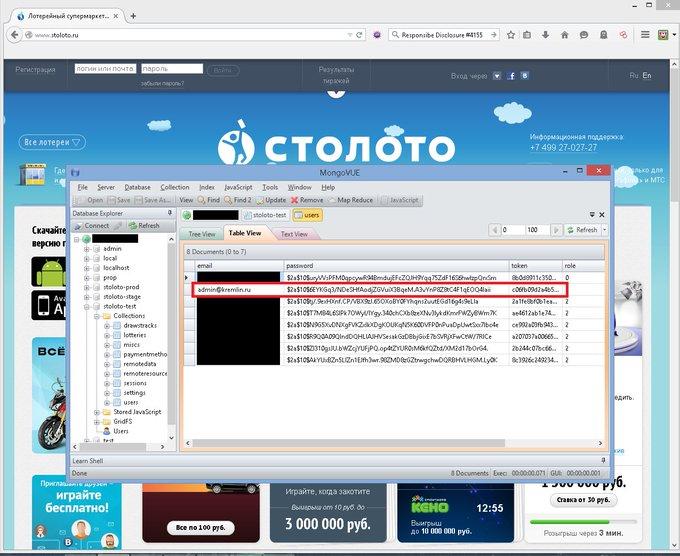
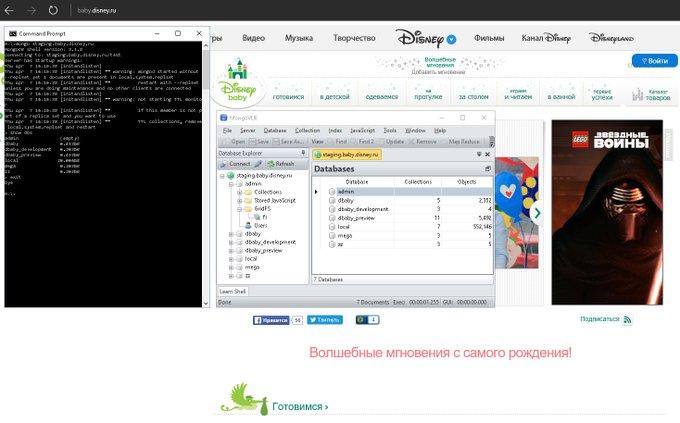
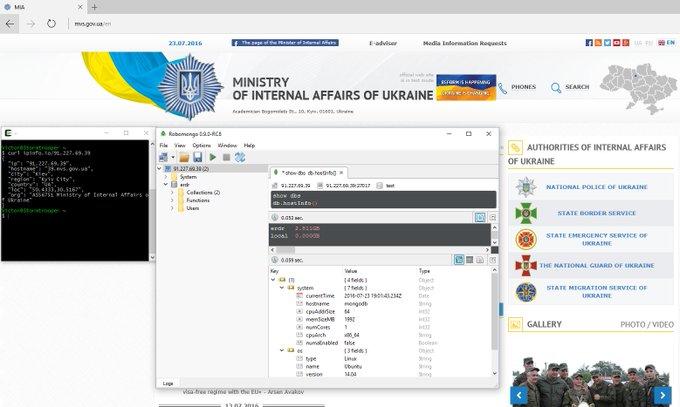
Flashing HDD firmware is a prerequisite for the snooping, the paper says, because the ATA protocol does not expose the PES. This could be accomplished through traditional attack techniques – binary exploitation, drive-by downloads, or phishing – or by intercepting HDDs somewhere in the supply chain and modifying them. The researchers point to the Grayfish malware attributed to the Equation Group as an example.
[…]
One limiting aspect of the described technique is that it requires a fairly loud conversation in the vicinity of the eavesdropping hard drive. To record comprehensible speech, the conversation had to reach 85 dBA, with 75 dBA being the low threshold for capturing muffled sound. To get Shazam to identify recordings captured through a hard drive, the source file had to be played at 90 dBA. Which is pretty loud. Like lawn mower or food blender loud.
The researchers acknowledge this is louder than most practical scenarios but they say they “expect that an attacker using state of the art filtering and voice recognition algorithms can substantially amplify the channel’s strength.”
While the growing popularity of solid state drives diminish the risk even further, there were still twice as many hard drives sold with PCs in 2017 as there were solid state drives, the researchers claimed.
[…]
They also note that their work may open future research possibilities, such as using a hard disk’s read/write head as a crude sounds generator to issue spoken commands to nearby connected speakers like Alexa, Google Home, and Siri.