As our planet warms up and rain patterns shift, the feathers and skin of many species are changing colors, often getting lighter. Snails in the Netherlands are going from brown to yellow. In a species of tropical bee in Costa Rica, the proportion of orange to blue individuals is increasing. Lizards in France are turning lighter, and so are many insects and birds across the globe. “Under global warming one would expect that the darker species, and darker individuals, might decline,” says Stefan Pinkert, an ecologist and evolutionary biologist at Yale University.
[…]
Melanins, the most common pigments in birds and mammals, may be affected by rising temperatures and changing rain patterns. “If you have more melanin in your skin or your fur or feathers, then it tends to absorb more heat,” says Matthew Shawkey, an evolutionary biologist at Ghent University in Belgium. This may be a disadvantage as the temperature soars, he says, because it can cause animals to overheat. On the flip side, if it rains more, pathogens tend to thrive. In such conditions, dark melanins can be protective because they “toughen up tissues,” Shawkey says.
A rule proposed by Charles Bogert, an American herpetologist, in a 1949 paper, predicts that hotter climates should have a higher presence of ectotherms, or so-called cold-blooded animals, that are lighter in color and therefore less likely to overheat. (These animals, such as reptiles and insects, can’t regulate their own body temperature, and they rely on external heat sources.)
In recent years, science has not only confirmed Bogert’s rule but also extended it to endothermic, or warm-blooded, species. It’s not just frogs, toads, snakes and midges that are lighter in warmer regions; birds get lighter as well. A 2024 analysis of more than 10,000 species of birds showed that in hot places, white and yellow feathers win over blue and black ones.
[…]
With global warming, some animal populations are becoming even lighter. Between 1967 and 2010, as temperatures in the Netherlands rose by 1.5 to two degrees Celsius, brown land snails gave way to yellow ones. Between 1990 and 2020 in the U.K., dragonflies and damselflies got progressively lighter, too—as Pinkert and his colleagues found in a 2023 paper. And if you’ve looked closely at some dragonflies, you may have noticed that they now have fewer dark ornaments on their wings.
In one recent study conducted in North America, male dragonflies from 10 different species had the smallest melanin-based color patches on their wings in the warmest years between 2005 and 2019. In this same time period, pretty spots also seemed to pale on Mediterranean Blue Tits—tiny birds with yellow chests and azure, hatlike markings on their head. Between 2015 and 2019, the blue head patches of tit populations around Montpellier, France, have gotten lighter by approximately 23 percent—a change related to the rise in local temperatures.
[…]
Besides individual ability to adjust color based on temperature, animal populations living in warming regions may become lighter simply because paler animals move into new areas. There may be genetic changes at play, too, Pinkert says, but we still have “a critical knowledge gap” about how such evolution may be playing out.
While Bogert’s rule appears straightforward in regions that heat up yet remain dry, such as the Mediterranean, if rainfall increases alongside temperatures, species may turn dark instead of light.
[…]
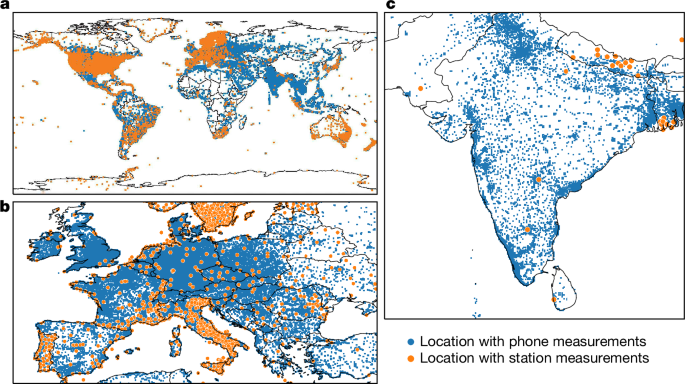
When Delhey tested what happens when both temperatures and precipitation increase with climate change, he found that, at least in birds, “the effects of humidity are generally much, much stronger,” he says. Delhey and his colleagues mapped the plumage colors of all species of passerine birds, of which there are more than 5,000, to climates in which they live. They found that the animals were lighter where warm and dry but darker where warm and humid. Roulin and his colleagues found something similar in a 2024 study of thousands of museum specimens of barn owls collected across the globe between 1901 and 2018. The researchers showed that over time, plumage colors became lighter where the climate got warmer and drier but darker where both temperature and precipitation increased. “Where the climate change was stronger, the change in color was stronger,” Roulin says.
[…]